Whether a startup or a global enterprise, all businesses must be compliant year-round and undergo an annual evaluation to avoid hefty fines. One important compliance is the Payment Card Industry Data Security Standard or PCI DSS that is mandated by credit card companies for all organizations handling cardholder information.
As a small or medium enterprise, it’s likely that you’ve heard of PCI DSS. However, do you comprehend what it is, why it is important, or whether you need it? No matter where you are in your PCI compliance journey, this article can be your springboard as you fulfill the 12 requirements of PCI compliance.
What Is PCI Compliance?
Put simply, Payment Card Industry (PCI) Compliance is mandated by credit card companies to help ensure the security of credit card transactions in the payments industry. Visa, MasterCard, American Express, Discover, and JCB formed the PCI Security Standards Council (PCI SSC) due to the escalating risks related to credit card fraud. They administer the Payment Card Industry Data Security Standard (PCI DSS), a set of requirements intended to warrant that all companies that process, store, or transmit credit card data maintain safe payments worldwide. It was launched in 2006 to manage PCI security standards and improve account security throughout the transaction process.
Is It Important?
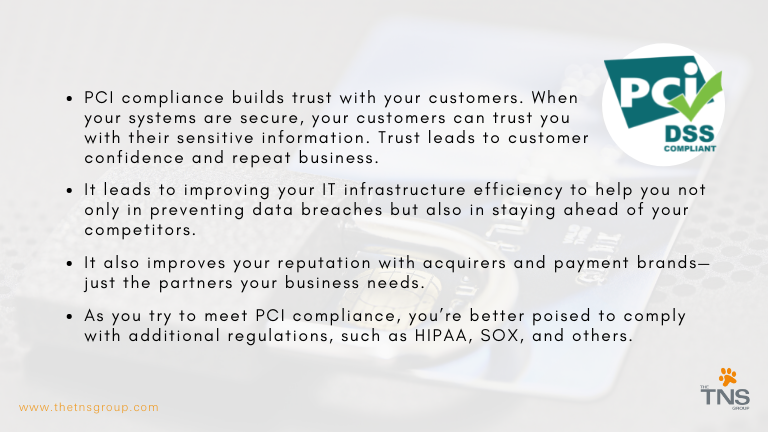
Daunting as it may seem, PCI compliance is now more important than ever as we embrace the age of digital consumption. Having the right tools and a trusted Managed Services Provider (MSP) to guide you along the way can make the process manageable. Our security experts at The TNS Group can help your organization reap the following benefits of achieving PCI compliance.
Do I Need to Comply with the PCI DSS?
All merchants and service providers must comply with the PCI DSS. The standard outlines four merchant levels that vary according to the number of transactions processed annually and have different reporting requirements. You can read more about PCI DSS merchant levels here.
What If I Don’t Achieve Compliance?
Failure to achieve PCI compliance can mean damage to your brand, costly forensic audits, and hefty penalties. The card brands can impose fines to your acquiring bank anywhere between $5,000 – $100,000 per month. The acquiring banks then pass these fines onto you. Repeated violations can lead to complete revocation of your privileges to accept card payments. Depending on where a data breach occurs and who it affects, the government can also impose fines that can shut down your business.
The 12 Requirements for PCI DSS Compliance
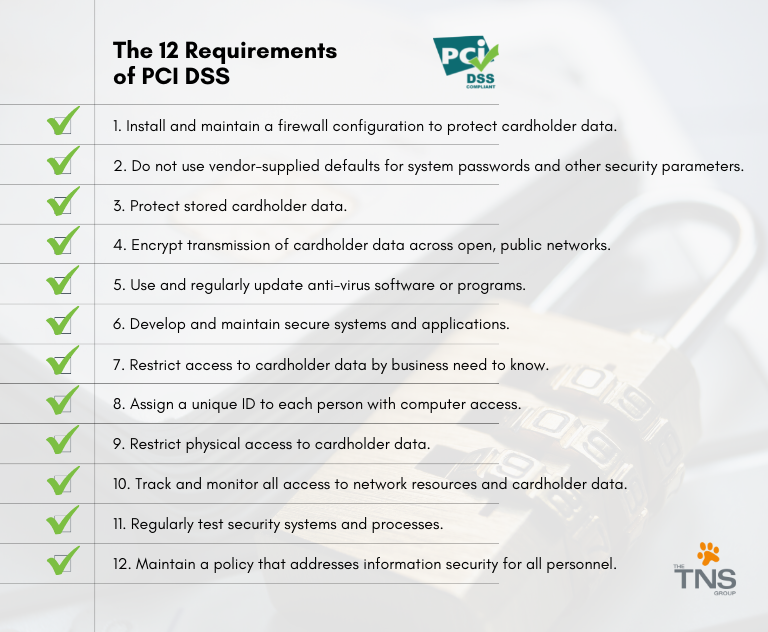
1. Use and Maintain Firewalls
Firewalls are required for PCI DSS compliance because of their usefulness in preventing unauthorized access. Firewalls block access of foreign or unknown entities attempting to access private data. These prevention systems are often the first line of defense against bad actors.
2. Protect Passwords
This involves keeping a list of all devices and software that require a password or other security to access. Vendor-supplied default settings are easily exploitable—they must be changed, and unnecessary default accounts disabled or removed before any system is installed on a network.
3. Protect Cardholder Data
Card data must be encrypted with certain algorithms. These encryptions are put into place with encryption keys, which are also required to be encrypted for compliance. Regular maintenance and scanning of primary account numbers are needed to ensure no unencrypted data exists.
4. Encrypt Transmitted Data
Cardholder data is sent across multiple ordinary channels (i.e., payment processors, home office from local stores, etc.). This data must be encrypted whenever it is sent to these known locations. Account numbers should also never be sent to locations that are unknown.
5. Use and Maintain Anti-Virus
Anti-virus mechanisms must be maintained and kept actively running and should only be disabled if formally authorized for a specific purpose. Anti-virus software is required for all devices that interact with and/or store primary account numbers. This software should be regularly patched and updated.
6. Update Software
Firewalls and anti-virus software will require regular updates. These updates are especially required for all software on devices that interact with or store cardholder data. It is a good idea to ensure that the anti-virus system is updated automatically, and administrative access is in place so that anti-virus can’t be disabled or altered by users.
7. Restrict Data Access
Cardholder data is required to be strictly confidential. All staff, executives, vendors, and other third parties who do not need access to this data should not have it. The roles that do need sensitive data should be well-documented and regularly updated.
8. Use Unique IDs for Access
Employees who have access to cardholder data should have individual credentials and identification for access. There should not be a single login to the encrypted data with more than one employee using the username and password.
9. Restrict Physical Access
Any cardholder data must be physically kept in a secure location. Both data that is physically written or typed and data that is digitally kept should be locked in a secure room, drawer, or cabinet. Not only should access be limited, but anytime the sensitive data is accessed, it should be kept in a log to remain compliant.
10. Create and Maintain Access Logs
Probably the most common non-compliance problem is the lack of proper recordkeeping when it comes to accessing sensitive data. All activities dealing with cardholder information require documentation. Compliance requires having audit logs that track every action taken by someone with administrative privileges, failed login attempts, and changes to accounts. Software products to log access are also needed to ensure accuracy.
11. Scan and Test for Vulnerabilities
There are several things involved in the above requirements that can malfunction, go out of date, or suffer from human error. These threats can be limited by fulfilling the PCI DSS requirement for regular scans and vulnerability testing.
12. Document Policies
Inventory of equipment, software, and employees that have access will need to be documented for compliance. The logs of accessing cardholder data will also require documentation. How information flows into your company, where it is stored, and how it is used after the point of sale will also all need to be documented.

PCI DSS compliance is not a walk in the park—no matter how pure your intentions may be. The process of reaching PCI compliance takes time and can seem like an overwhelming list of requirements, but it’s ultimately what will spell the difference between a failed cyberattack and a cyber incident that hurts your business. Despite the challenges, you should strive to comply with PCI DSS, because failure to do so can have significant setbacks.
If you have any questions on how security, protection, and compliance can help you grow your business while saving money, contact The TNS Group today. Let’s discuss your specific PCI DSS Audit requirements or other security services sooner rather than later.
Share this blog post with your colleagues and friends. Follow The TNS Group on Facebook, Twitter, Instagram, or LinkedIn.
Categories: Managed Service Provider, MSP Blogs, Solution Blogs




