
If cybercrime were a country, it would be the world’s third-largest economy after the U.S. and China!
The rate at which businesses today are experiencing cybersecurity hacks and breaches is alarming. According to Cybersecurity Ventures, cybercrime is expected to cost the global economy $10.5 trillion by 2025, reflecting a 15% increase yearly.
Some of 2022’s biggest cybercrimes include the Crypto.com hack, Ronin Crypto Theft, Microsoft Data Breach, Red Cross Data Breach, and Cash App Data Breach. For small to medium businesses (SMBs), lessons learned from these recent cyberattacks can inform your cybersecurity strategies for next year.
- Crypto.com, an online platform for trading cryptocurrency, was hacked on January 17. Cybercriminals targeted 483 crypto wallets by going around the 2-factor authentication (2FA) and removing $30+ million in cryptocurrency. The company was forced to reimburse the attacked accounts. The perpetrators weren’t found, and no group has ever claimed responsibility for the attack.
- The biggest cyberattack of this year (and the second-largest crypto hack of all time) happened between November 2021 to March 2022. Ronin’s Axie Infinity game that allows earning digital currency dialed back security protocols so its servers could handle a growing player base. Cybercriminals took advantage of that and stole $600+ million in cryptocurrency.
- On March 20, 2022, the international cybercrime group Lapsus$ posted a screenshot on Telegram indicating they had hacked Microsoft and, in the process, compromised Cortana, Bing, and several other products. The attack on Microsoft was not about stealing personal information or money. Rather, the attackers wanted to damage the company’s reputation.
- In January, the cyberattack on Red Cross compromised 500+ thousand records of “highly vulnerable people,” frequently victims of war and possible witnesses. This information could be sold to international crime rings, which often target these people. Authorities couldn’t identify the assailant, and the organization placed its servers offline for some time to prevent further attacks and remove the vulnerability.
- In April, the attack on Cash App, a popular payment tool, didn’t come from a previously unknown digital vulnerability or a cybercrime campaign. Rather, a disgruntled former employee accessed the company’s servers and compromised the names, trading information, and stock portfolios of 8+ million users. This information could allow digital crime organizations to access user bank accounts, conduct identity theft, and gain entry to social media accounts.
Size doesn’t matter! Hackers don’t care how big or small a target you are—they prefer to look for vulnerabilities that can be easily and quickly exploited. They simply want to expose and take advantage of gaps in legacy systems and backdoor vulnerabilities and steal valuable data. Thinking you’re too small to be noticed can be a dangerous assumption.
To guard against the next security breach and the implication to your reputation, you need to make cybersecurity a priority before it’s too late. Partner with a reputable Managed IT Services Provider (MSP) to guarantee a multi-layered approach to security while you stay focused on your primary business objectives.
Here, we’ve compiled ten top cybersecurity tips and best practices for you to implement and share with your team.
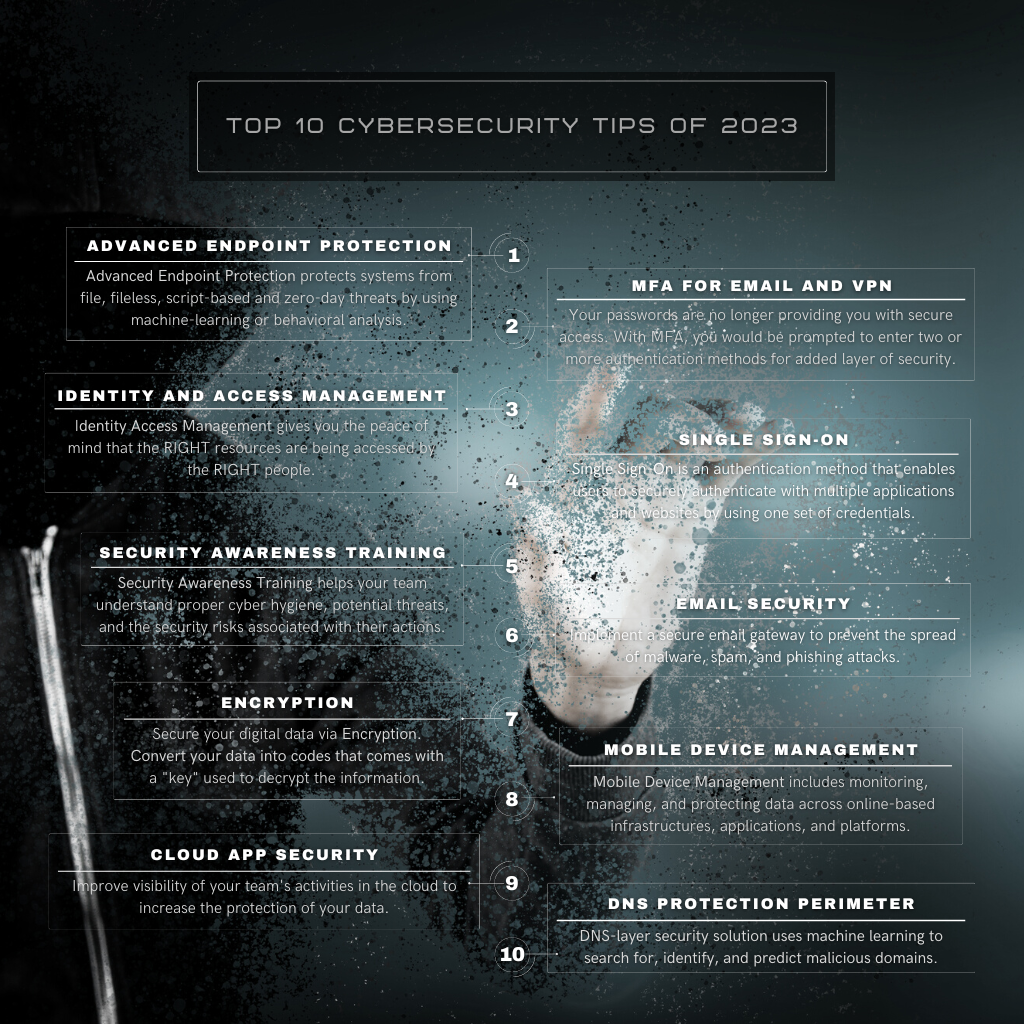
1. Advanced Endpoint Protection
The number of endpoints has increased exponentially for all organizations that have shifted to remote work. Having 50 employees working in separate locations means you need to consider each location an extension of your business. TNS’ Advanced Endpoint Protection is designed to proactively stop specific types of threats, tools, or techniques, covering multiple stages of cyberattacks.
2. MFA for Email and VPN
Passwords are no longer enough! Supplement your traditional password with Multi-Factor Authentication (MFA)—something you HAVE and something you KNOW. With MFA, your team would be prompted to enter more than two additional authentication methods for an extra layer of security. Identity theft takes on many forms, and you need to insist that your users have another form of confirming their identity when accessing your corporate network.
3. Identity and Access Management
Implement solutions to protect your data from unauthorized access by internal and external users. Just because your systems are in the cloud does not mean certain people within your organization shouldn’t have access to specific things. Our Identity and Access Management will allow us to work with you so you can have the peace of mind that the RIGHT people are accessing the RIGHT resources.
4. Single Sign-On
Reduce the chances of having your team’s passwords and sensitive data stolen in a breach. Single Sign-On (SSO) is an authentication method that enables users to securely authenticate using just one set of credentials with multiple applications and websites. It streamlines the process of signing on and using applications—no need to re-enter passwords, leads to fewer chances of phishing, and lessens password-related complaints or troubles for IT help desks.
5. Security Awareness Training
Strengthen your most vulnerable access point, i.e., your employees, against cyberattacks through effective Security Awareness Training (SAT). Your team members are now an essential layer of your defense strategy; keeping them informed keeps your organization safe. Simulated vulnerabilities deployed through an MSP increases your employees’ awareness and, more importantly, protects your company’s data. TNS can help your team understand proper cyber hygiene, anticipate potential threats they may encounter via email and the web, and realize the security risks associated with their actions.
6. Email Security
Implement a secure email gateway to prevent the spread of malware, spam, and phishing attacks. There are various procedures and techniques for protecting email accounts, content, and communication against unauthorized access, loss, or compromise. They can be as simple as removing all executable content from emails to more comprehensive actions, like sending questionable content to a sandboxing tool for detailed analysis. Your MSP will have visibility into all emails being sent and can enforce email encryption policies to prevent sensitive information from falling into the wrong hands.
7. Encryption
With email encryption services, you can securely transmit data to other parties and reduce the risk of disseminating it. TNS’ encryption platforms work by taking the sensitive data out of your emails and locking it in a secure web portal. When you send an encrypted email, it’s sent to the cloud, and your recipient gets an email notification that an encrypted email awaits them on the website. They can only access it by authenticating with an approved username and password or a one-time code. You can set the email to expire after a given time, so if a malicious party has access to their username and password, it will still be safe, as the link will be dead.
8. Mobile Device Management
The inherent risks associated with Bring Your Own Device (BYOD) have generated the need for Mobile Device Management (MDM) solutions to monitor, manage, and secure employees’ mobile devices. Implementing MDM into your environment will allow you to reap the benefits of BYOD and limit the risks. MDM solutions can proactively secure mobile devices by specifying password policies, enforcing encryption settings, selectively wiping corporate data, and streamlining the device setup. No matter the device or the team member’s location, MDM software allows your MSP to secure corporate data and personal data.
9. Cloud App Security
Improve the visibility of your team’s activities in the cloud on all your devices to increase the protection of your data. TNS’ Cloud App Security natively integrates with your Microsoft and third-party cloud services to provide simple deployment, centralized management, and innovative automation capabilities. Your MSP can identify high-risk usage and security incidents, detect abnormal user behavior, and prevent threats. We can also set encryption rules to protect data stored in and downloaded from the cloud.
10. DNS Protection Perimeter
Protecting your Domain Name Services (DNS), also known as DNS Protection Perimeter, is a solution that can help you avoid hackers before they sneak into your systems and do irreversible damage. DNS-layer security solution uses machine learning to search for, identify, and predict malicious domains. It allows you to limit your team from visiting unauthorized websites that could put your company at risk and helps you manage and alter your organization’s web filter at will across the network.
Implementing a layered approach to security allows for extra protection for your company data while staying within your budget. It’s your Managed Service Provider’s job to know which solutions work for you and why. Contact your Account Manager directly to learn more. If you are currently not a TNS partner, complete our contact form and select Managed IT Services as your service of choice or contact us at 203-316-0112 or 212-967-5757.
Share this blog post with your colleagues and friends. Follow The TNS Group on Facebook, Twitter, LinkedIn, YouTube, or Instagram.
Categories: Managed Service Provider, MSP Blogs, Solution Blogs




